One Way SSL Mulesoft Configuration
craft software
Last Update 4 yıl önce
Introduction
In one-way SSL authentication, the server application shares its public certificate with the client. In a two-way authentication, the client application verifies the identity of the server application, and then the server application verifies the identity of the client application. Sometimes two-way SSL is also known as Mutual Authentication.
In this article, we will be going to learn how to set up the one-way SSL and two-way SSL for MuleSoft applications.
One Way SSL
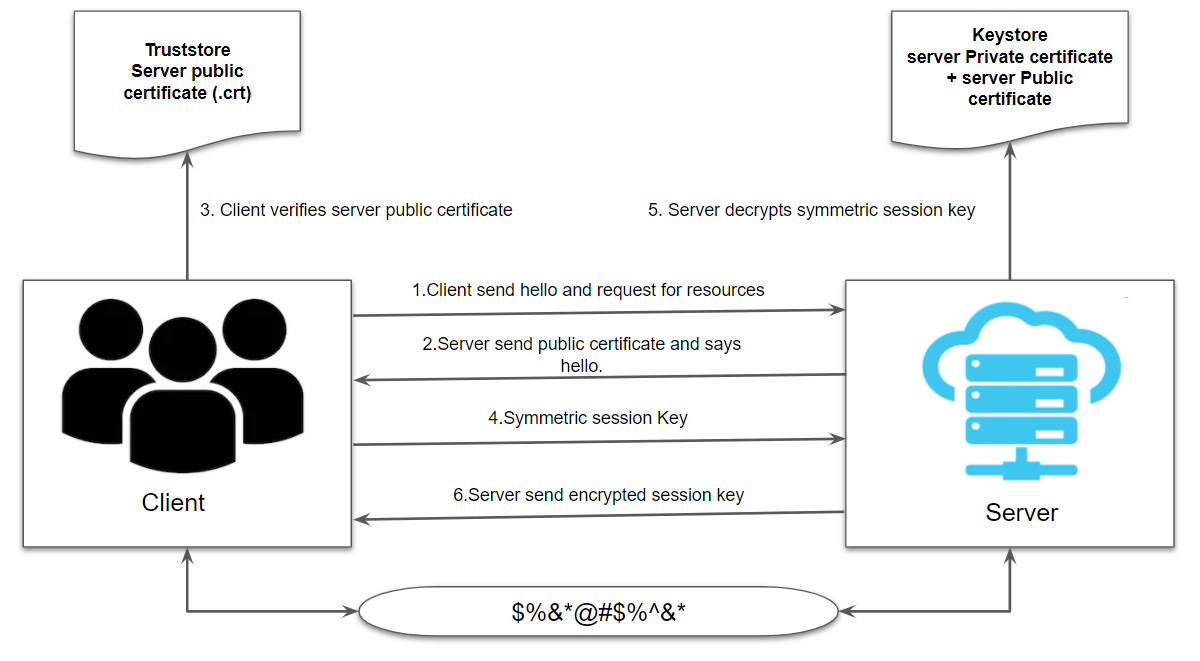
As mentioned above in one way SSL only client verifies the server certificates. At the server end, there will be a Keystore that will hold the private and public certificate of the server whereas, at the client end, there will be a truststore that will hold the public certificate of the server.
- Clients will send Hello and request for the resources on the secure HTTPS protocol.
- The server will respond with its public certificate (.crt) and send Hello.
- The client will verify the server public certificate in its truststore.
- The client sends back symmetric session key generated using the server public certificate.
- The server will decrypt the symmetric session key using its private certificate and send back the encrypted session key to the client for establishing a secure connection.
Implementing One Way SSL For MuleSoft Application
For generating Keystore and truststore, we can use OpenSSL or keytool utility. For this article, we will be using keytool which is part of your JDK.
Step 1: Generate Server Keystore
For generating Keystore, we will be using the below command.
Once we execute the above command, it will ask for the Keystore password, first and last name including other details and the key password.
alias in the above command is used to search the certificate in the Keystore as there can be multiple certificates in the same Keystore and alias is useful in identifying the right certificate.

Step 2: Export the Public Certificate From Server Keystore
We will be requiring the server public certificate to be installed in the client truststore. So we need to extract the public key from the server Keystore.
For extracting the server public certificate, we will be using the below export command.
This command will export the server public certificate and we will import that server public certificate in the client truststore.

Step 3: Import Server Public Certificate Into Client Truststore
For importing the server public key into the client truststore, we will be using the below command.
This above command will generate the client's truststore and import the server public certificate.

Now, we have generated the server Keystore and client truststore.
Step 4: Configuring MuleSoft HTTP Listener and Requester
Let's see how we can configure Keystore and truststore on the MuleSoft application.
Now, we will configure the server-Keystore on the MuleSoft HTTP Listener. Under General Settings, the Protocol must be "HTTPS". We need to make sure server-Keystore.jks and client-truststore.jks that are generated in the above steps, must be copied under folder src/main/resources.

This is the configuration that needs to be done on the server-side.
Now, we will see the client-side configuration. For that, we will be using the MuleSoft HTTP requester. Provide the connection settings on the HTTP requester.

Now, we will do the TLS configuration. Provide the client's truststore path, password, type, etc.


